Why vendor-risk management must be every organization’s primary concern?
Before the pandemic arrived, critical services were already increasingly being handled by third-party vendors. With the advent of COVID-19, remote work has become a commonly accepted practice globally. These two factors have multiplied the risk of cyberattacks and third-party data breaches. Mobile Computer Services, a managed IT service company, explains third-party or vendor risks that plague organizations currently and shares some ways to counteract or manage this threat.
Understanding vendor risk management
Third-party risk management (TPRM), or vendor risk management (VRM), is the process of mitigating threats that may arise from a third-party vendor such as HR, payroll, web development, design, and other service providers that provide products or services to the organization or its customers. Every time these service providers are granted remote access to an organization's network, a new threat vector is created.
Third-party risk management also includes controlling costs and mitigating risks that can be associated with using an outside entity.
Third-party ecosystems are complex and fast-paced, but they are indispensable to a business that seeks to stay ahead of the competition and expand. A vendor risk management program allows a company to manage and monitor all its vendors and interaction by developing multi-faceted programs that secure the networks.
Here are a few reasons why a successful vendor risk management program is beneficial for both companies and vendors:
- Eliminates costly operational failures
- Exceeds compliance with HIPAA, OCC, GDPR, and PCI DSS
- Prepares companies for regulatory mandates
- Lessens the threat of bankruptcy
- Reduces third-party breach costs
Common access points that pose security risks include connections such as security systems with cameras, building management systems (lighting or video surveillance), printers, HVAC, and even thermostats. Other points could be connected machines, assembly devices, unattended robots, or operating systems that are using a non-standard port to communicate to an organization’s network.
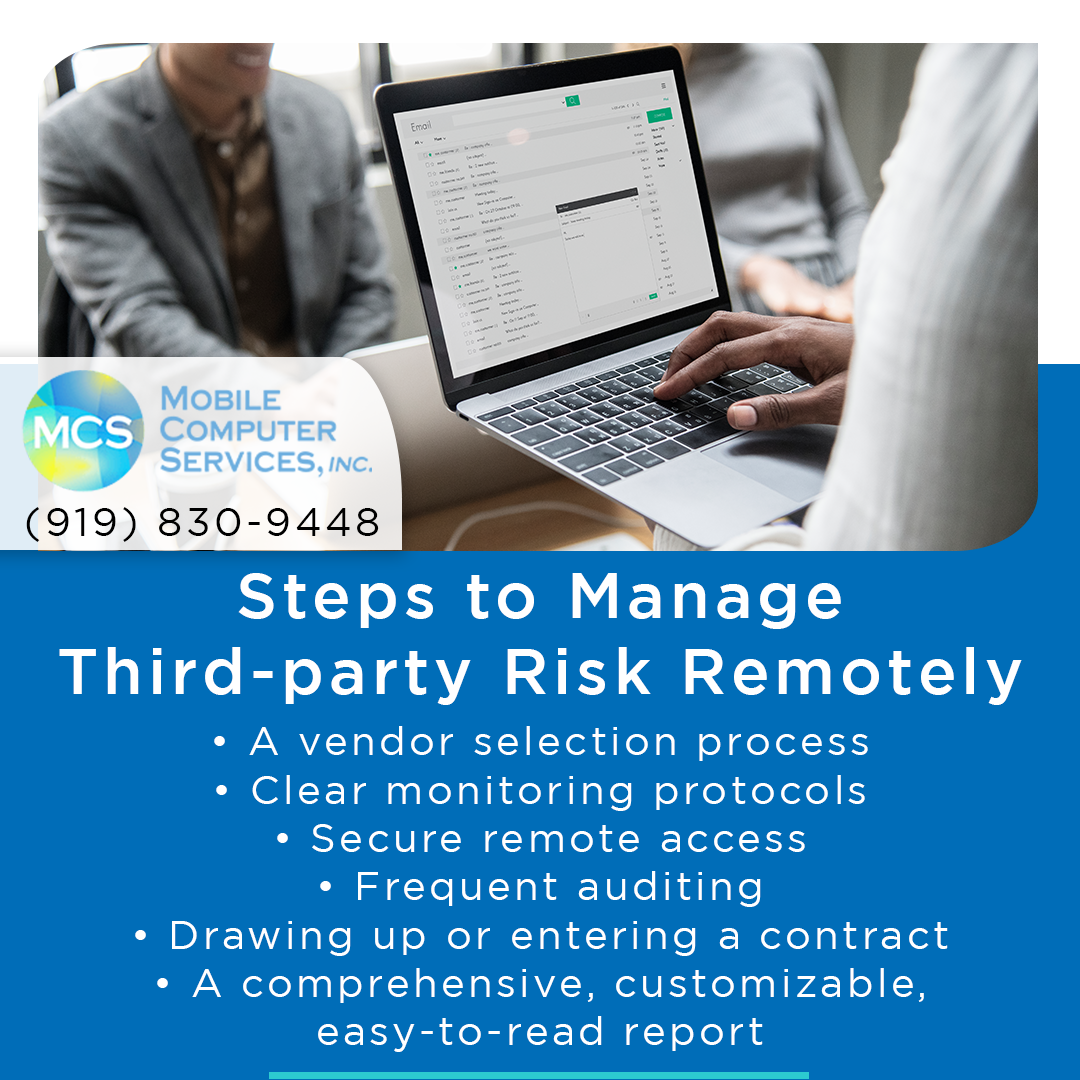
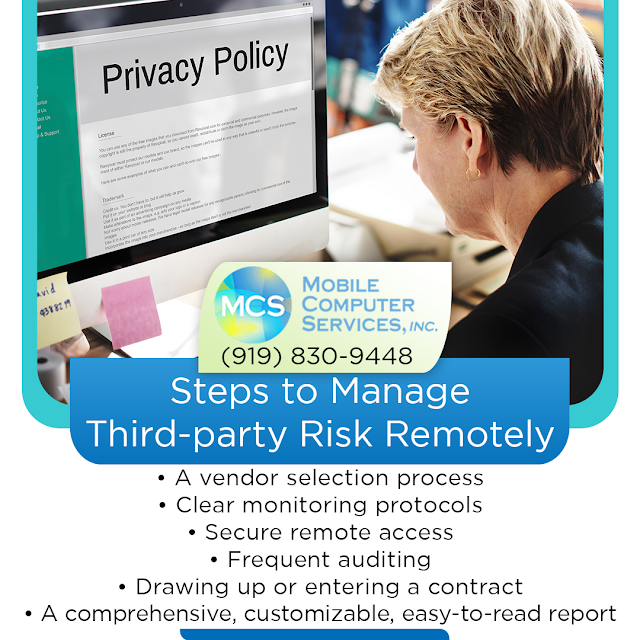
Steps to manage third-party risk remotely?
- A vendor selection process that includes complete risk assessment including reputational risk, operational risk, and data risk. The up-front check on these risks needs to be agreed upon to protect the organization from strategic and financial risks. A vendor management team can be tasked with finding the right vendors that are in alignment with company policies and objectives.
- Clear monitoring protocols must be established for devices, data, and all third-party transactions during remote work. Employees need to comply completely with the protocols while the vendors must provide a regular report.
- Secure remote access software can help businesses mitigate threats and identify the point of breach. This can help businesses streamline and solidify their cybersecurity and IT processes.
- Frequent auditing of the plan by the IT team, CTO, or consultant can ensure all standards are maintained and are current.
- Drawing up or entering a contract with a third-party vendor with clauses or amendments that allow for check-ins. Non-compliance with data security would entail a breach of the contract or trigger changes. Therefore, some key performance indicators (KPIs) and other contractual landmarks must be emphasized in the contract.
- A comprehensive, customizable, easy-to-read report should be easily accessible to management and appropriate staff when necessary.

Why Mobile Computer Services?
Mobile Computer Services is a professional IT services company that works with small and medium-sized businesses in Raleigh NC. The services include:
- Managed IT services - 24x7 proactive monitoring and management of the company's IT infrastructure.
- Network services: Comprehensive care for the network systems provided by certified technicians.
- Business continuity planning: Get the business back on its feet swiftly during and after disasters.
- IT consulting: High-caliber advice from professional consultants to help achieve business goals.
- Security: Safeguard business from malicious hackers and cyber attacks.
- On-demand services: Day or night, the dedicated support staff is always available to assist.
- Office move: Professional office relocation and network cabling services.
- VoIP: Reduce telecom expenses and improve communications with powerful phone systems.
- Email Protection: Protect mail systems from spam and malware.
Contact Mobile Computer Services, Inc. at Raleigh NC today at (919) 830-9448 to find out about its Managed IT services.